Organizations worldwide, on average, implement over a hundred business-critical software solutions annually. This reliance on software makes global enterprises vulnerable to cyberattacks and security breaches.
In response, companies are becoming increasingly security-conscious when choosing a software vendor—especially for a solution that will help them strengthen connections with clients or customers.
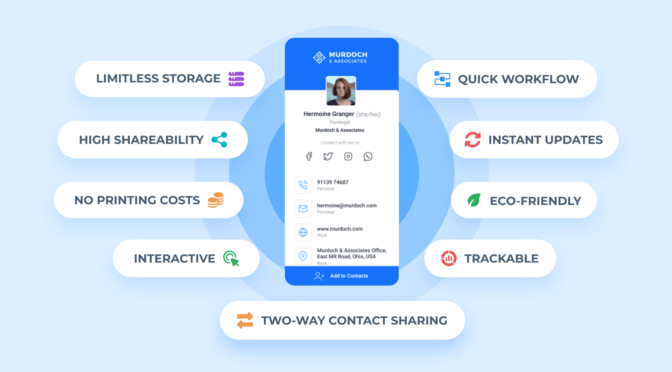
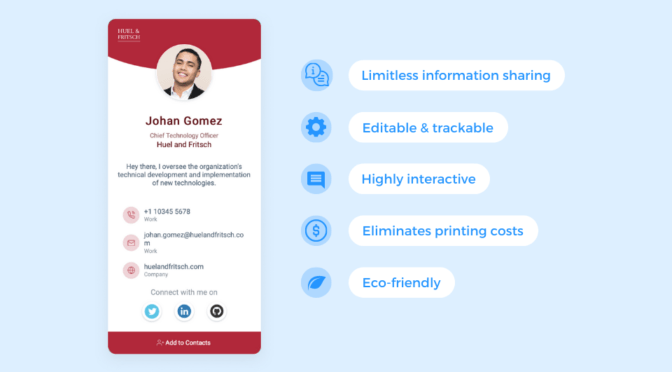
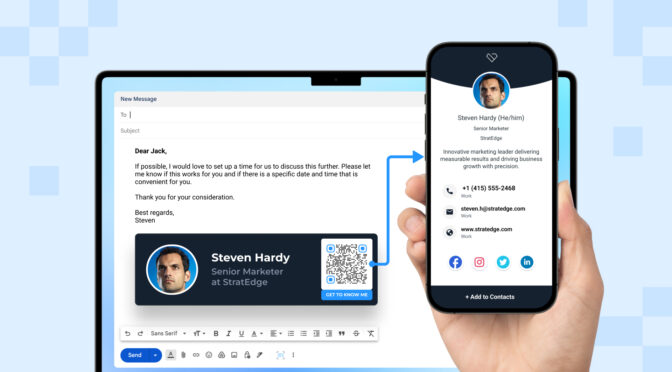
Among these solutions, digital business cards (or e-business cards) are witnessing widespread use across industries. Countless individuals and organizations are now switching to digital business cards to create meaningful customer connections and conduct ROI-driven networking.
Digital business cards hold confidential user information (also known as PII—Personal Identifiable Information). Hence, before choosing a platform to conduct your e-business card activities, you must first qualify that platform’s capacity to safeguard your organization’s data.
But which security methodologies and features should you look for to decide on a truly secure digital business card platform?
Keep reading to learn the eight key security factors to consider when choosing the most secure digital business card solution.
Table of contents
- 8 factors to consider when choosing a secure digital business card solution
- Choosing the most secure digital business card solution on the planet
- Frequently asked questions
8 key factors to consider when choosing the most secure digital business card solution
So, how do you determine if a platform holds itself to the highest standards when it comes to trust and security?
Below are the eight critical security measures a digital business card solution must implement to guarantee maximum security for its customers:
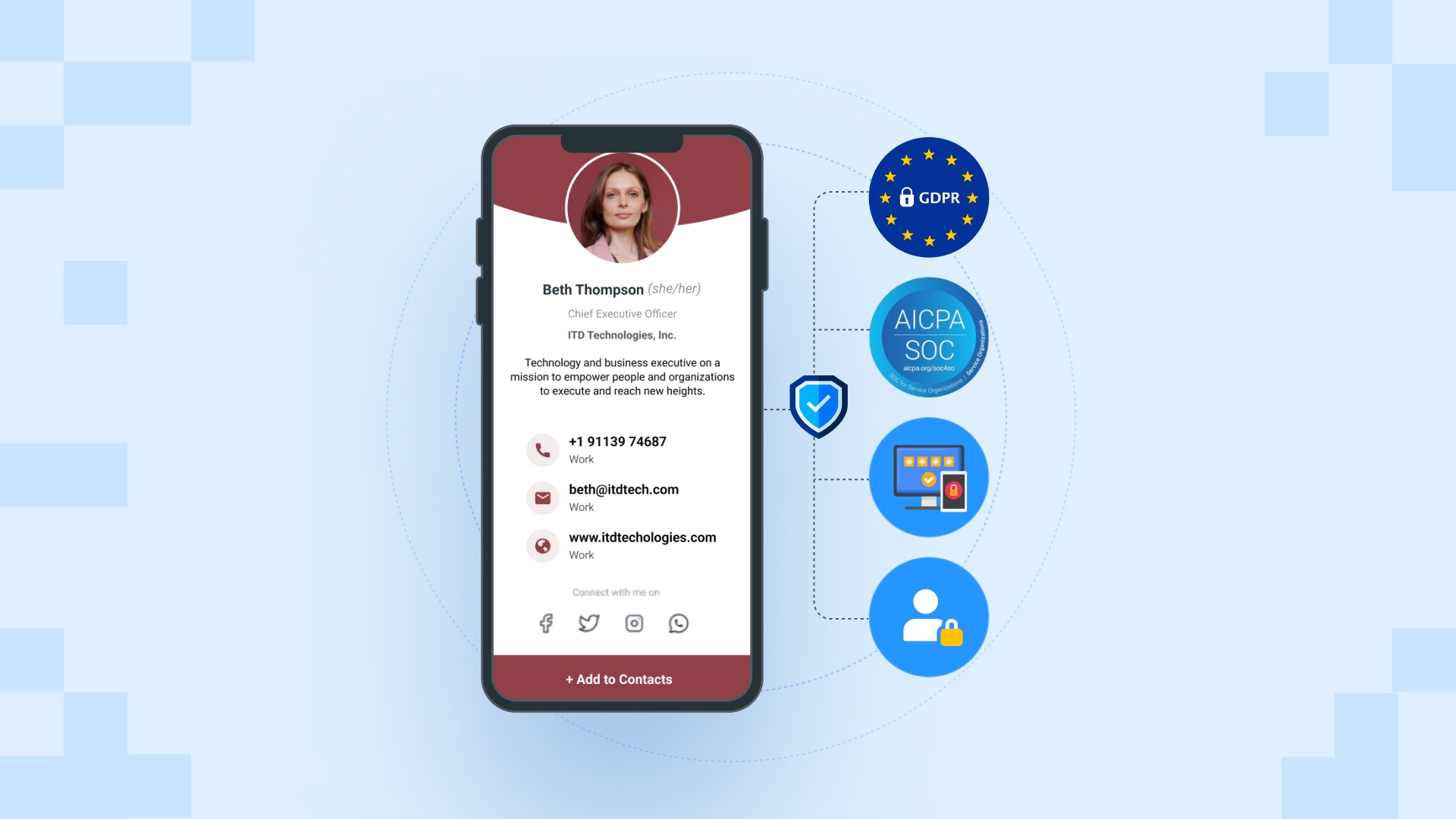
- GDPR and SOC 2 Type 1 & Type 2 compliance
- Strong data encryption capability
- Periodical security penetration testing
- Phishing URL detection
- SSO authentication
- Multi-factor authentication and password protection
- Multi-user access management
- Data interference protection
#1 GDPR and SOC 2 Type 1 & Type 2 compliance

A recent study revealed that in 93% of cases, an external attacker could breach an organization’s network and access its resources.
This is why top cybersecurity regulators are always improving their criteria when assessing the security of a software solution.
Two of the most widely accepted and rigorous security compliance standards globally are GDPR (General Data Protection Regulation) and AICPA’s SOC 2 (Service Organization Control).
Both of these regulated security standards provide a framework that companies can follow to securely store and protect client and end-user data.
While GDPR compliance is mandatory for most companies, not all solutions comply with SOC 2 standards. Why? Attaining the latest SOC 2 certification (Type 2) is no easy feat. It takes significant investment, strategic planning, and organization. This is the reason why many companies opt out of the process of attaining this compliance.
Uniqode (formerly Beaconstac) is the first digital business card solution to become SOC 2 Type 1 and Type 2 certified, in addition to already being GDPR compliant. This demonstrates the platform’s commitment to meeting the highest privacy and security standards.
#2 Strong data encryption capability
Before investing in a digital business card solution, you must ensure the platform has the capacity to encrypt your organization’s employee and customer data.
Data encryption protects any PII—whether that PII is internal (inside your organization) or external (submitted by your users)—from being accessed by malicious individuals and entities.
At Uniqode, we use 256-bit AES to encrypt data at rest. For data in transit, we secure network communications with TLS 1.2 encryption. These two algorithms are among the best encryption methods for shielding confidential data from security breaches.
#3 Periodical security penetration testing
Digital business card platforms handle massive amounts of confidential information. Hence, they must periodically evaluate the overall security of their IT infrastructure. This is where penetration testing (or pen testing) becomes crucial.
This proactive cybersecurity measure simulates actual cyberattacks against a computer system. The aim is to reveal exploitable vulnerabilities within the infrastructure so they can be addressed accordingly.
This testing ensures the e-business card solution’s internal system can defend itself against the biggest privacy and security threats.
You might want to know: Pen tests are part of GDPR and SOC 2 compliance. It is in itself rigorous to perform, which is why only 75% of companies conduct it.
Since Uniqode is both GDPR and SOC 2 compliant, it undergoes regular penetration tests to uncover vulnerable spots in its system and eliminate them immediately—ensuring maximum data protection for our users.
#4 Phishing URL detection

Phishing attacks are rising and becoming more sophisticated, making it crucial for security-centric digital business card solutions to implement phishing URL detection.
This security feature enables a platform to recognize phishing websites that are linked to a digital business card.
Through this capability, a platform can disable any digital business card connected to a phishing URL as soon as that URL is reported by a user. The platform then adds the URL to a database of blacklisted web pages for future reference. This entire phishing URL detection framework protects users—at all levels—from accessing fraudulent links.
#5 SSO authentication

Single Sign-On (SSO) allows your team members to log in and authenticate only once to access your organization’s various software solutions.
With SSO, employees log in once and only use one set of credentials, so your organization significantly reduces the likelihood of password leaks and identity theft.
Uniqode’s SSO capabilities make use of the powerful SAML 2.0 protocol. This feature ensures that users can log in to the dashboard securely using their organization’s credentials—without compromising identity and security.
#6 Multi-factor authentication and password protection
Multi-factor authentication requires your employees to go through an added level of authentication—in addition to a password—to access your organization’s e-business card platform. This extra layer of security significantly reduces the risk of password compromise.
Password protection, on the other hand, ensures that only authorized users can access your employee’s cards.
Uniqode is one of the few solutions that offer password-protected digital business cards. With this security feature, users can ensure their digital business cards are only accessible to their target audience.
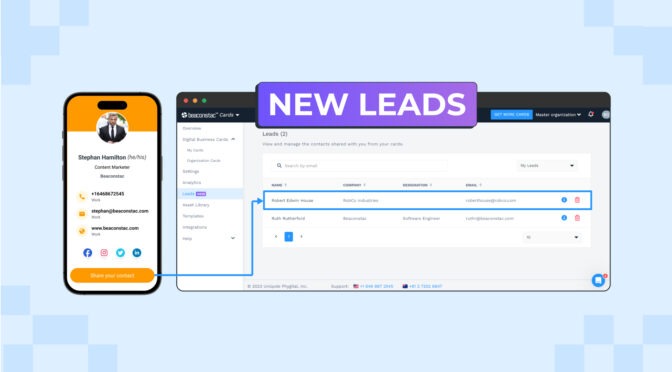
#7 Central management and role-based access
Central management gives you complete control of your organization’s digital business card creation and deployment.
For instance, a solution’s central management feature may allow you to enforce branding guidelines and set team access to certain features and functionalities. You can even suspend cards from team members who are no longer a part of your company.
Uniqode’s central management capabilities empower you to conveniently oversee your organization’s digital business cards and their associated networking activities—from a single dashboard.
1. Create sub-accounts for your teams
2. Set user permissions (role-based access)
3. Discontinue cards for ex-team members
4. Enforce branding guidelines across each card in your company, and more
With central management, you can prevent unauthorized card use, making your company’s networking activities much more secure.
Note: Central management features starts with our BUSINESS plan.
#8 Data interference protection
An e-business card maker may provide card-scan tracking to let organizations monitor their digital business cards’ engagement performance.
However, unwanted interference from hackers might attempt to distort this engagement data, resulting in inaccurate metrics (such as an exaggerated scan number from one location).
As a countermeasure, a secure digital business card solution will set up a robust anomaly detection protocol within their infrastructure.
This protocol ensures the protection of card-scan metrics from bot interference, preventing the generation of misleading data.
Uniqode takes a precise approach when protecting digital business cards from bot interference. The platform identifies and filters abnormal scan behavior from your digital business card’s analytics, leaving you with accurate metrics to gauge the effectiveness of your networking efforts.
Choose the most secure digital business card solution on the planet
Once you decide to pivot to digital networking, it is imperative to choose a digital business card solution that can provide maximum security for your organization and its customers.
Currently, Uniqode is the only solution that implements all the security measures discussed above. These industry-leading and enterprise-grade security measures—practiced in unison—ensure complete protection against cyber threats and data compromise.
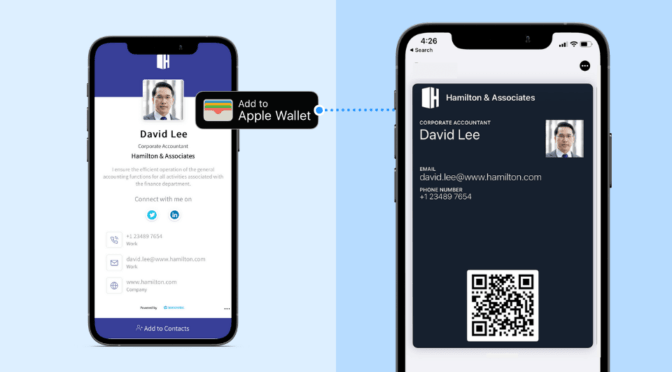
In addition to taking these security measures, Uniqode provides the ability to create and manage digital business cards at scale and share them contact-free via Apple or Google Wallet for ROI-driven networking.
All of these advanced capabilities are accessible without downloading an app.
Further reading: The 6 Best Digital Business Card Solutions Available Today

Frequently asked questions
Are digital business cards secure?
Today’s leading digital business card solutions implement and prioritize various measures to ensure the security of their digital business cards and end users. These security procedures include GDPR and SOC 2 compliance, regular security audits, centralized card management, and more.
Does Uniqode encrypt personally identifiable information (PII)?
Yes. Uniqode uses powerful encryption algorithms to ensure that any personally identifiable data within its system remains private. These algorithms prevent unauthorized users from accessing your organization and end-user data and keep your networking activities safe and secure.
Why do organizations trust Uniqode’s digital business card solution regarding data privacy and security?
Uniqode constantly strives to uphold the industry’s highest privacy and security standards. And as a result, thousands of leading global businesses trust our platform to meet their advanced security requirements.
To satisfy these requirements, Uniqode employs various security solutions—going above and beyond with SOC 2 Type 2 compliance and rigorous security audits. Our employees strictly adhere to the best security practices and undergo annual cybersecurity awareness training. This practice ensures user data—at all levels—stays private and is safeguarded from exploitation, misuse, or loss.